How to sign up ?
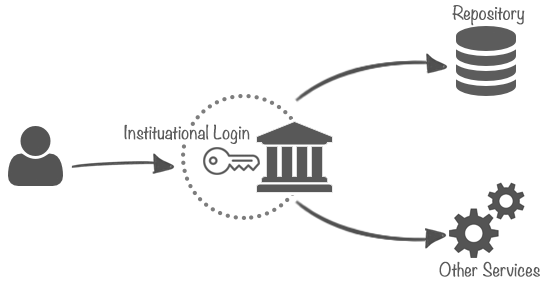
We are very glad that you are using our services and that you want to further the experience by obtaining an account. There are basically two paths possible, the preferred and more convenient for both you and us is logging with an institutional account. Below there's an overview of the institutional logins and local logins; both with directions how to obtain the account.
1. Institutional Login
With institutional logins you are de facto logging to a familiar page of your home institution and you are using credentials you already remember. The full procedure is bit more complicated - you initiate the login at our service, you are redirected to your institution and only after successfully logging there you are redirected back. Your insitution acts like a sort of a proxy for the multitude of services available in all the CLARIN Centres.
2. Your Institution is not Listed
In case your institution is not listed (but please try searching all the available countries and maybe also using the english name of your institution) the preffered approach is to create an account with CLARIN. After you obtain your account, proceed to login with institution called "Clarin.eu website account".
3. Local Accounts
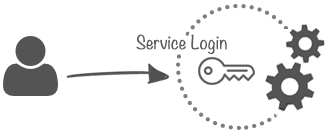
With a local account you will gain access to only one service, the one you've asked for. When you discover a different service in our infrastructure you'll need to ask again and again. The same goes for services in other eu countries - you'll need to ask and ask and ask. Now it might not seem as that much when you think only one service, but when you think the whole infrastructure it means remembering login/password combination for each of these services. If you are convinced that this is what you need or have some other reason for wanting a local account please This email address is being protected from spambots. You need JavaScript enabled to view it..
Supported Organisations
From where you can login to our services
In order to allow access from all over the world, LINDAT/CLARIN service provider is a member of several identity federations including CLARIN SPF and eduGAIN. Unfortunately, some of these federations include identity providers who do not guarantee their users to be real people (e.g., you can trace the account to an email but not to a person). We try to keep our services as open as possible but there are cases (e.g., signing licenses in our repository) where anonymous users are forbidden.
For that reason we choose to exclude users from test IdPs and from IdPs that let you create your accounts online with no further background check.
We are blocking the following IdPs:
- https://openidp.aco.net/saml
- https://idp.protectnetwork.org/protectnetwork-idp
- https://mojeid.cz/saml/idp.xml
- https://umbrellaid.org/idp/shibboleth
- Everyone having entity category http://refeds.org/category/hide-from-discovery
The implementation in shibboleth is illustrated below (snippets from shibbolet2.xml)
<!-- CLARIN SPF - Metadata about all IdPs in participating Identity Federations -->
<MetadataProvider type="XML" uri="https://infra.clarin.eu/aai/prod_md_about_spf_idps.xml">
<MetadataFilter type="Blacklist">
<Exclude>https://openidp.aco.net/saml</Exclude>
</MetadataFilter>
</MetadataProvider>
<!-- edugain -->
<MetadataProvider type="XML" uri="https://metadata.eduid.cz/entities/edugain+idp">
<MetadataFilter type="Blacklist">
<Exclude>https://idp.protectnetwork.org/protectnetwork-idp</Exclude>
</MetadataFilter>
<MetadataFilter type="Blacklist" matcher="EntityAttributes">
<saml:Attribute Name="http://macedir.org/entity-category" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:uri">
<saml:AttributeValue>http://refeds.org/category/hide-from-discovery</saml:AttributeValue>
</saml:Attribute>
</MetadataFilter>
</MetadataProvider>
Logging out
All logouts are application level only
When you click a logout button in any of our applications you are logged out from that application only; the sp session and idp session are still active. In practice this means when you try to log in again you might not be able to select an idp (the one you've used the last time is remembered) or you might not be asked to enter username/password on your idp page (if you select the same idp, the idp remembers you for some time). You can get more information about why single logout is hard at Shibboleth wiki.
If you need to share your machine (eg. for a presentation) use anonymous/incognito mode of the browser or close the browser (not just a tab); additionaly you might want to remove the cookies.